Assured control.
Mission resilience.
Propolis establishes hard boundaries and continuity protocols for volatile communications and aerospace environments. Engineered for sovereign structural integrity.
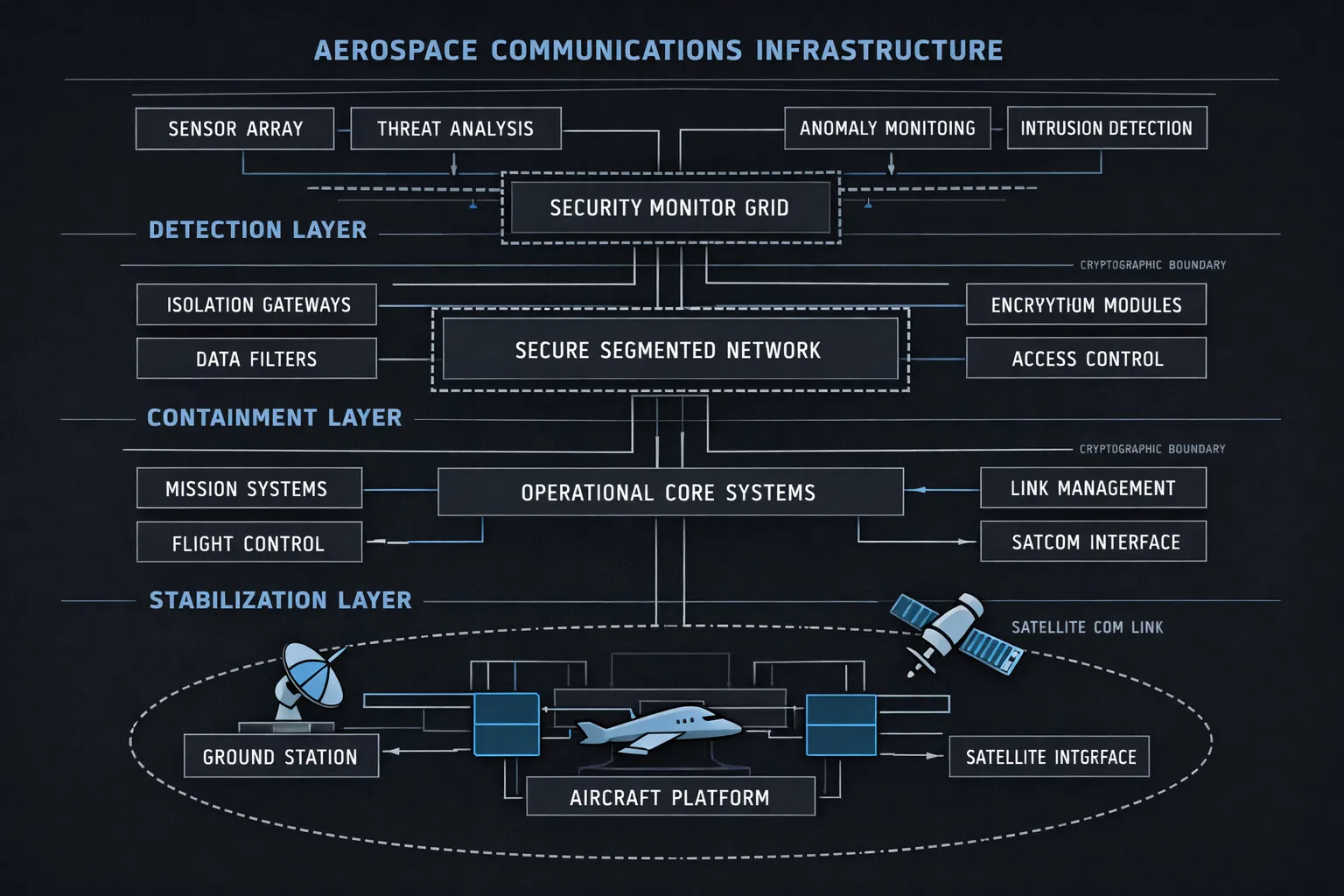
Detection and containment
Total state isolation for volatile subsystem parameters. Hard physical and cryptographic boundaries prevent degradation propagation across mission-critical networks.
Detection
Subsystem anomaly flagged and logged to telemetry matrix.
Containment
Hard isolation boundaries engaged. Node quarantine enforced.
Stabilisation
Network state restored to verified nominal parameters.
Abstract network simulation
Real-time visual abstraction of a live containment event. Isolated nodes are highlighted via controlled signal pathways, verifying programmatic isolation under hostile data influx conditions.
Cascading failure prevention objective
Simulated resilience preservation
Verified containment under modelled conditions
Engineered infrastructure
Multi-layered detection, containment, and stabilisation architecture. Cryptographic boundaries enforce hard isolation across detection, containment, and operational core systems.
Validated baseline metrics
Operational validation programmes
Northern Enclave
High-latitude air-gapped environment. Evaluates signal attenuation and isolation integrity under extreme atmospheric conditions.
Orbital Resilience
Low-Earth Orbit mesh simulation. Models high-energy spectral interference and autonomous node-mesh recovery protocols.
Secure Transmission Layer
Cryptographic packet routing baseline. Performance verification of lattice-based hardware encryption under sustained multi-terabit traffic influx.
Initiate a technical programme discussion
Direct access to the PROPOLIS technical directorate. Engagement is reviewed for operational suitability and programme alignment.
Or contact directly:
[email protected]